After we read the post about Istalling IIS Services, continue with Using New IIS Services, and previous post about Hosting Applications, now time for final chapter post titled Managing IIS 7.5. The biggest improvement in IIS 7 .5 is in the area of management. Windows Server 2008 R2 includes a number of IIS configuration tools that were previously available only as separate downloads, and Microsoft has enhanced many of the existing tools.
Automating IIS administration with Windows powerShell
As in many other areas of the Windows Server 2008 R2 operating system, Microsoft is emphasizing Windows PowerShell as an important tool for managing IIS 7.5. The IIS PowerShell snapin provides dozens of new cmdlets and enables administrators to manage IIS properties in several different ways.
Selecting Windows PowerShell Modules from the Administrative Tools program group loads the system modules included with Windows Server 2008 R2, including the WebAdministration module that provides the IIS functionality. You can also import the module manually from any Windows PowerShell prompt by using the following command:
Import-Module WebAdministration
Once you have access to the IIS Windows PowerShell snap-in, you can display all of the cmdlets it contains by using the following command:
Get-Command –pssnapin WebAdministration
The snap-in uses three different types of cmdlets, as follows:
- PowerShell provider cmdlets
- Low-level configuration cmdlets
- Task-oriented cmdlets
These cmdlet types correspond to three different methods of managing IIS from the Windows PowerShell prompt, as described in the following sections
Using the IIS powerShell provider
The IIS PowerShell provider creates a hierarchical IIS namespace that administrators can navigate just like a file system directory structure. When you type iis: and press Enter at a Windows PowerShell prompt (with the WebAdministration module imported), the prompt changes to PS IIS:> and typing the dir command displays not the file system, but the top level of the IIS namespace, as follows:
Name
----
AppPools Sites SslBindings
After changing to the Sites directory with the cd Sites command, the dir command displays a list of the IIS sites on the server, as follows:
|
Name
|
ID
|
State
|
Physical Path
|
Bindings
|
|
----
|
--
|
-----
|
-------------
|
--------
|
|
Default Web
|
Site 1
|
Started
|
%SystemDrive%\inetpub\wwwroot
|
http *:80:
|
The Get-Item cmdlet enables you to display selected sites in the same format. By piping the results of the Get-Item cmdlet to the Select-Object cmdlet, you can display all of the properties of a selected site,
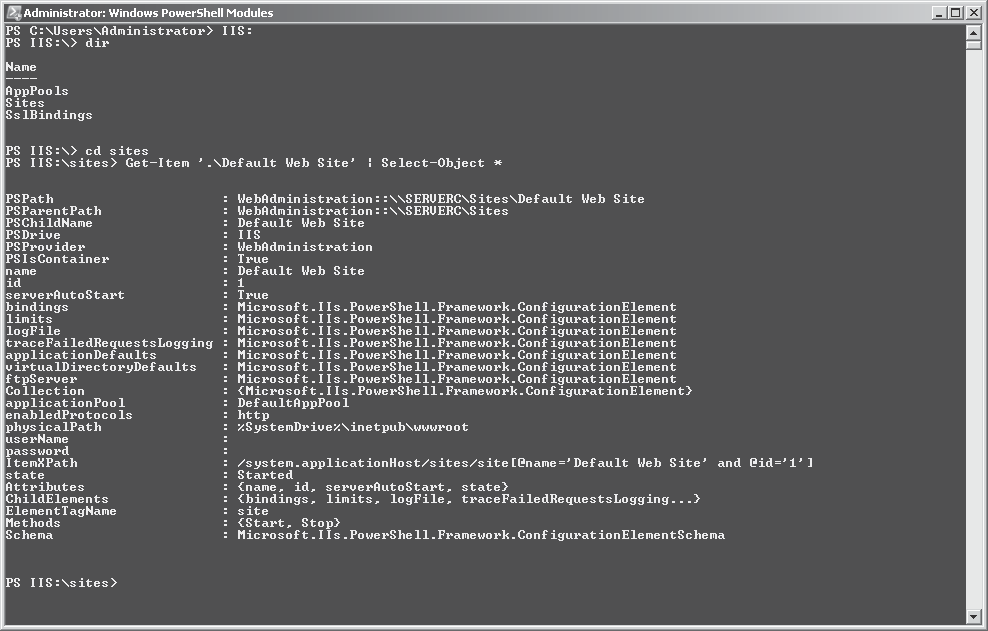
Generic cmdlets such as Get-Item and Select-Object are part of the standard Windows PowerShell interface. Any module that includes a provider hierarchy must support them. Once within the IIS hierarchy, you can use low-level configuration cmdlets to manage specific IIS elements without having to type extended path names.
Using Low-Level Configuration Cmdlets
IIS 7.0, first released as part of Windows Server 2008, represents a complete revision of the IIS architecture, and extensibility was a major priority of that revision. This new architecture, carried over into the IIS 7.5 release in Windows Server 2008 R2, is schema driven and uses XML-based configuration files, which are two major contributing factors to its complete extensibility. This extensibility complicates the process of developing a Windows PowerShell management strategy, however. Cmdlets might have static parameters that enable them to manage specific properties of an element, but if a third-party developer creates an IIS extension that adds new properties to that element, the existing cmdlets cannot manage them.
Therefore, the IIS Windows PowerShell snap-in includes low-level configuration cmdlets that you can use to view and manage all of the hundreds of IIS configuration settings, including custom settings added by IIS extensions. One set of these low-level cmdlets, concerned with IIS configuration elements, is as follows:
- Add-WebConfiguration, Adds a collection element to an existing IIS configuration collection
- Backup-WebConfiguration, Creates a backup of an IIS configuration
- Clear-WebConfiguration, Removes configuration settings from the specified loca- tion
- Get-WebConfiguration, Gets an IIS configuration element at a specified location
- Restore-WebConfiguration, Restores IIS configuration elements from a previously executed backup
- Select-WebConfiguration, Returns Web configuration objects
- Set-WebConfiguration, Sets an IIS configuration element to a specified value
Using task-Oriented Cmdlets
In addition to the low-level configuration cmdlets, the IIS Windows PowerShell snapin includes a large collection of cmdlets designed to simplify common IIS maintenance tasks, such as creating, removing, starting, and stopping specific IIS elements. One set of task- oriented cmdlets, concerned with managing IIS sites, is as follows:
- Get-Website
- New-Website
- Remove-Website
- Start-Website
- Stop-Website
Unlike the low-level cmdlets, the task-oriented cmdlets do not rely on the IIS namespace (although they can utilize it), and they use static parameters to configure specific properties . For example, to create a new Web site, you might use a command like the following:
New-Website –Name Intranet –Port 80 –HostHeader intra.example.local –PhysicalPath "$env:systemdrive\inetpub\intranet" -Ssl
This command creates a new site with the name Intranet, using the default port number value 80, and using the host header value intra.example.local to differentiate this site from other sites that use the same address and port number. The Web site will use content files located in the \inetpub\intranet folder on the computer’s system drive, and it will allow users to connect with SSL encryption by using the HTTPS: prefix in their URLs.
Once you have created the site, you can even use the Windows PowerShell interface to create new content . After switching to the site directory in the IIS hierarchy with the command cd\sites\Intranet, you can use the following command to open a Notepad window containing a new Index .html file:
notepad "$(Get–WebFilePath .)\index.html"
Using IIS administration pack extensions
The IIS Administration Pack is a downloadable collection of extensions for IIS 7.0. In Windows Server 2008 R2, most of the contents of the Administration Pack are included in the IIS 7.5 implementation. For example, the ASP .NET and FastCGI configuration capabilities described earlier in this chapter were originally part of the Administration Pack, and are now incorporated into the default user interface of the Internet Information Services (IIS) Manager console in Windows Server 2008 R2. Also accessible through the console are the features described in the following sections .
Using Configuration editor
Configuration Editor is a graphical tool that enables administrators to view and manage any setting in any of the IIS configuration files. Because the tool is based on the IIS configuration schema, it can even manage custom settings without any interface modifications. In addition, once you have performed your modifications, the Configuration Editor can generate a script that duplicates those modifications for execution on other servers.
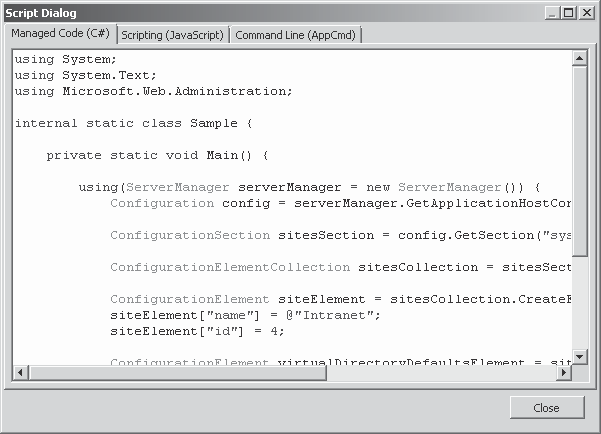
For example, you can use Configuration Editor to create a new IIS site, setting the same parameters as the New-Website Windows PowerShell cmdlet if desired. To do this, you open the Configuration Editor in the Internet Information Services (IIS) Manager console at the server level and, in the Section drop-down list, select system .applicationHost/sites.
When you open the Collection Editor window, you see the server’s existing Web sites and an interface for creating a new one, you can configure a multitude of settings for the new site, after which it appears as part of the collection
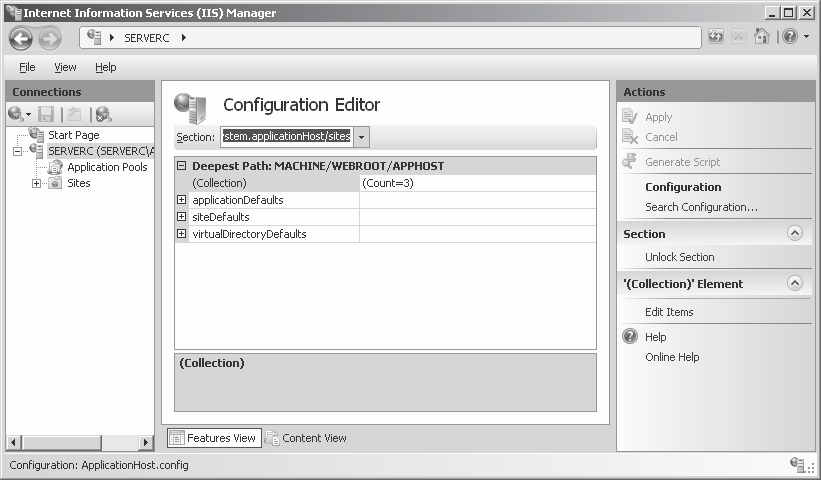
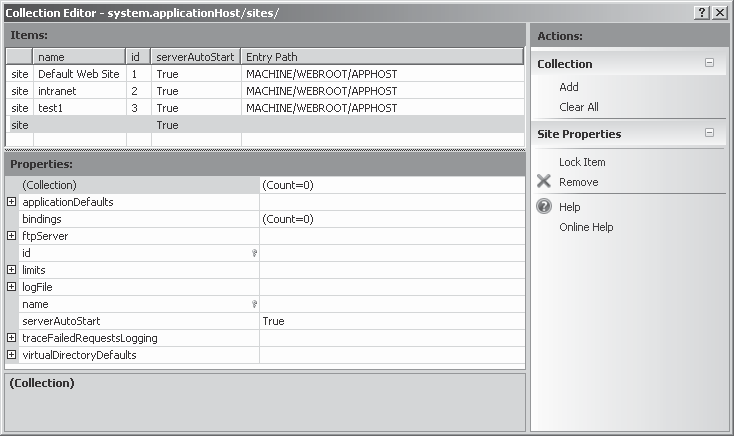
Finally, back on the Configuration Editor page, clicking Generate Script in the Actions pane displays script code that will create a new site identical to the one you just added, using managed code (C#), JavaScript, or the Appcmd .exe program at the command prompt, from this window, you can copy the code to a text file to save for later use.
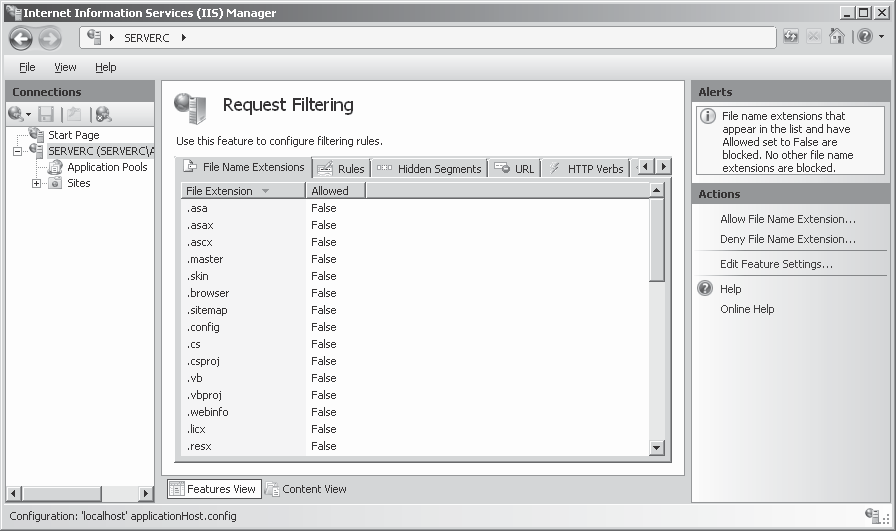
Using request Filtering
The Request Filtering module integrates the capabilities of a separate product called Microsoft Urlscan Filter 3 .1 into the default Internet Information Services (IIS) Manager console in Windows Server 2008 R2. Request Filtering is essentially a graphical interface that inserts code into Web .config files that limits the type of HTTP requests a particular IIS server or site will process. Requests that the filtering mechanism rejects are logged with error codes that indicate the reason for the rejection.
The Request Filtering page, contains seven tabs that enable you to create the following types of filters:
- File Name Extensions, Filters incoming HTTP requests based on the extension of the file requested . For example, to prevent IIS from serving any Active Server Pages files, you would add a Deny File Name Extension entry, using the extension .asp.
- Rules, Filters incoming HTTP requests based on rules that specify text strings that cannot appear in the URL, a query string, or the HTTP header of a request for a par- ticular file extension.
- Hidden Segments, Filters incoming HTTP requests based on specific segments of a URL. For example, this enables you to filter out requests for files in the bin folder with- out rejecting requests for files in the binary folder.
- URl, Filters incoming HTTP requests based on specified character strings in the requested URL.
- HTTP Verbs, Filters incoming HTTP requests based on the verb specified in the HTTP message.
- Headers, Filters incoming HTTP requests based on size limits for particular HTTP header values.
- Query Strings, Filters incoming HTTP requests based on specific query strings. This capability is particularly useful in preventing SQL injection attacks, in which query strings contain escape characters or other damaging code.